How Hackers Steal Cryptocurrency
Published: 12 Feb 2026
Cryptocurrency is exciting, but it can also be risky. Many people invest their hard-earned money, only to lose it in seconds because of hackers. Most beginners don’t even realize how easy it is for criminals to steal crypto. That’s why it’s important to understand how hackers steal cryptocurrency and how you can protect yourself before it’s too late.
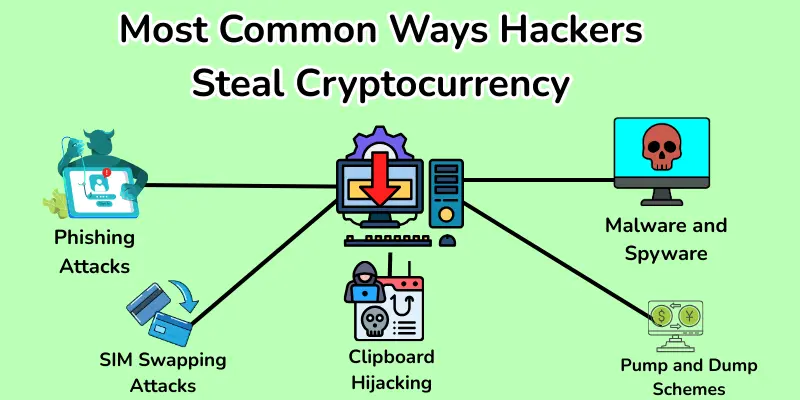
Most Common Ways Hackers Steal Cryptocurrency
Hackers use many smart and hidden methods to steal cryptocurrency from users. Knowing these common ways can help you stay alert and protect your digital assets.
- Phishing Attacks
- Malware and Spyware
- Fake Crypto Wallets and Apps
- Exchange Hacks
- SIM Swapping Attacks
- Social Engineering Scams
- Clipboard Hijacking
- Smart Contract Exploits
- Rug Pulls and Exit Scams
- Pump and Dump Schemes
1. Phishing Attacks
Phishing is one of the most common ways hackers steal cryptocurrency. Hackers send fake emails, fake messages, or fake links. These look real, but they are not. Their goal is to trick you into giving your login details or private keys.
Hackers create emails and websites that look exactly like real crypto platforms. They may pretend to be an exchange, a wallet app, or customer support. When you click their link, it opens a fake website that steals your information.
- They copy real logos and designs.
- They use urgent words like “Your account is at risk.”
- They ask you to log in or verify your wallet.

How Users Get Tricked
Many users click links without checking the sender. Some people enter their passwords on fake pages. Others download fake apps. Hackers then access their wallets and steal their crypto.
- Users trust the message too quickly.
- They do not check the website URL.
- They share private keys or recovery phrases.
Always remember: Real companies never ask for your private keys or recovery phrases.
2. Malware and Spyware
Malware is bad software. It enters your device without your knowledge. Hackers use it to steal information. Two common types are keyloggers and trojans.
Keyloggers record everything you type. Trojans hide in fake apps or files. When installed, they give hackers full access.
- Malware hides in emails, downloads, or apps.
- It runs in the background.
- It secretly sends your data to hackers.

How Malware Steals Private Keys
Malware looks for wallet files and private keys. It copies your recovery phrase when you type it. It can also change wallet addresses when you send crypto.
- It steals keys when you log in.
- It copies phrases from notes or screenshots.
- It redirects payments to hacker wallets.
Always download apps only from official sources. Keep your device updated and safe.
3. Fake Crypto Wallets and Apps
Hackers make fake crypto wallets and apps. They look real. People download them by mistake. Once installed, hackers can steal all your crypto.
- Fake apps copy real logos and designs.
- They ask for passwords or private keys.
- They often promise “free crypto” or bonuses.
How Fake Wallets Steal Funds
When you enter your private key or recovery phrase, hackers get it. They can access your wallet instantly. Any crypto you send or store is stolen immediately.
- They can empty your wallet quickly.
- They track every transaction you make.
- You cannot reverse these transfers.
Always check the official website before downloading any wallet. Only use trusted and verified apps.
4. Exchange Hacks
Crypto exchanges are platforms where people buy and sell cryptocurrency. Hackers target them because they hold large amounts of crypto. Once hacked, users’ funds can be stolen in seconds.
- Hackers find weak spots in the platform.
- They exploit security loopholes.
- Sometimes, insiders help hackers steal funds.

Examples of Exchange Breaches
- Mt. Gox (2014): Hackers stole 850,000 BTC.
- Bitfinex (2016): Hackers took 120,000 BTC.
- KuCoin (2020): Hackers stole over $275 million.
These examples show that even big exchanges can be hacked.
Always enable 2FA and keep minimal funds on exchanges. Store most crypto in hardware wallets.
5. SIM Swapping Attacks
Hackers take control of your phone number. They trick your mobile operator. Once they get your SIM, they access your crypto accounts.
- Hackers call your mobile provider.
- They pretend to be you.
- They request a new SIM with your number.

How Hackers Access Crypto Accounts
After controlling your SIM, hackers receive 2FA codes sent by SMS. They log in to your wallets or exchanges easily. Then, they transfer your crypto to their accounts.
- They bypass SMS-based security.
- They steal funds within minutes.
- You may not notice until it’s too late.
Always use app-based 2FA instead of SMS. Never share your phone number with strangers online.
6. Social Engineering Scams
Hackers trick people into stealing crypto. They act friendly or official. Their goal is to make you share secrets.
- They pretend to be support agents.
- They claim you won a giveaway.
- They act like friends or influencers.
How Scammers Steal Crypto
Hackers ask for passwords, private keys, or recovery phrases. People trust them and give the info. Hackers access wallets and steal crypto instantly.
- They send fake messages or emails.
- They create fake profiles online.
- They promise rewards to get your info.
Always verify who you talk to online. Never share private keys or recovery phrases.
7. Clipboard Hijacking
When you copy a crypto address to send coins, hackers can replace it without you noticing. You think you are sending it to your friend. But the crypto goes straight to the hacker. Once it’s sent, you cannot get it back.
How It Works
Malware runs in the background on your computer or phone. When you copy a wallet address, it replaces it automatically. Users send crypto and lose it instantly.
- It works silently without your knowledge.
- Both hot and software wallets are at risk.
- Even small amounts can be stolen.
Always double-check wallet addresses before sending crypto. Use hardware wallets for extra safety.
8. Smart Contract Exploits
Smart contracts are programs on the blockchain. Hackers look for bugs or mistakes in the code. They use these flaws to steal crypto from users.
- Exploits happen mostly on DeFi platforms.
- Hackers attack contracts before developers fix bugs.
- Millions of dollars can be stolen quickly.
How Hackers Steal Crypto
Hackers find weak spots in smart contracts. They trigger the bug to move funds to their wallet. Users often lose all their crypto instantly.
- Exploits happen fast and silently.
- Users cannot reverse the transaction.
- Security depends on how well the contract is coded.
Always use trusted DeFi platforms. Avoid new or unverified projects.
9. Rug Pulls and Exit Scams
Hackers or dishonest developers create fake crypto projects. They attract investors with promises of high returns. Once they get enough funds, they disappear with all the money.
- Developers suddenly close the project.
- Investors cannot access their crypto.
- The money is gone forever.
How Users Get Tricked
Hackers promote the project online with fake ads and influencers. People invest without checking details. When the developers exit, all funds are stolen.
- They promise unrealistic profits.
- They fake reviews and testimonials.
- They push investors to act fast.
Always research projects carefully. Avoid new crypto projects without proof.
10. Pump and Dump Schemes
Hackers or scammers quickly inflate the price of a cryptocurrency. They make it look popular. When the price is high, they sell all their coins and disappear.
- The coin price drops instantly.
- Investors lost a lot of money.
- Scammers profit while others suffer.
How Users Get Tricked
Scammers promote the coin online with fake hype. People buy fast, hoping to earn. When scammers sell, investors are left with worthless coins.
- They use social media to create hype.
- They promise big profits quickly.
- They push people to act without thinking.
Always research coins carefully. Avoid coins with sudden hype or unrealistic promises.
Signs Your Cryptocurrency Has Been Hacked
If hackers access your crypto, there are clear warning signs. Recognizing them early can save your funds.
Signs:
- Unauthorized Transactions: Crypto moves without your permission.
- Locked Accounts: You cannot log in to your wallet or exchange.
- Missing Funds: Your balance is lower than it should be.
- Password Not Working: Your usual password suddenly fails.
- Unknown Devices Logged In: Suspicious devices show in the account history.
- Unexpected Emails: Alerts about changes you didn’t make.
- Unusual Activity Notifications: Notifications from the exchange or wallet you didn’t trigger.
Always act fast if you notice any of these signs.
What to Do If Your Crypto Gets Stolen
If hackers steal your crypto, act immediately. Fast action can reduce the damage.
Steps to Take:
- Stop Using Compromised Accounts: Log out and do not access hacked wallets.
- Change Passwords: Update all passwords for email, wallets, and exchanges.
- Enable 2FA: Add app-based two-factor authentication.
- Contact the Exchange: Report the theft to your crypto platform immediately.
- Report to Authorities: Inform local cybercrime or financial authorities.
- Check for Malware: Scan your device and remove any harmful software.
- Notify Trusted Contacts: Inform friends or collaborators if needed.
Always keep records of stolen transactions. This helps with reporting and investigation.
How to Protect Your Cryptocurrency from Hackers
You can keep your crypto safe by following these simple steps:
- Use Strong Passwords: Create long, unique passwords. Use a password manager. Never reuse passwords.
- Enable Two-Factor Authentication (2FA): Always use app-based 2FA. It adds extra security.
- Use Hardware Wallets: Store crypto in cold wallets offline. They are safe from hackers.
- Avoid Public Wi-Fi: Do not access wallets on public networks. Use a VPN if needed.
- Verify URLs and Apps: Check website addresses carefully. Download apps only from official sources.
- Keep Software Updated: Update wallets, apps, and devices regularly. Security patches protect you.
- Never Share Private Keys or Seed Phrases: Keep them secret. Never share with anyone.
Conclusion
So, friends, we are almost done. In this post, we covered How Hackers Steal Cryptocurrency. My advice is to always stay alert and protect your wallets. Use strong passwords, 2FA, and hardware wallets. Don’t wait, secure your crypto today and stay safe online.
FAQs about how Hackers Steal Cryptocurrency
Hackers use phishing, malware, fake wallets, or exchange hacks. They trick users into sharing passwords or private keys. Once they get access, they steal crypto instantly.
Hardware wallets are very safe. Hackers cannot access them online. But if someone knows your PIN or seed phrase, they can steal it.
Phishing is when hackers pretend to be real platforms. They send fake emails or websites to steal your login details.
Keep your device updated and secure. Only download apps from official sources. Use antivirus software and scan your device regularly.
Rug pulls happen when developers run away with investors’ money. They create fake projects and disappear with funds.
It is very hard to recover stolen crypto. Blockchain transactions are irreversible. Sometimes exchanges or authorities help, but recovery is rare.

- Be Respectful
- Stay Relevant
- Stay Positive
- True Feedback
- Encourage Discussion
- Avoid Spamming
- No Fake News
- Don't Copy-Paste
- No Personal Attacks

- Be Respectful
- Stay Relevant
- Stay Positive
- True Feedback
- Encourage Discussion
- Avoid Spamming
- No Fake News
- Don't Copy-Paste
- No Personal Attacks
